Integrated access management
Products
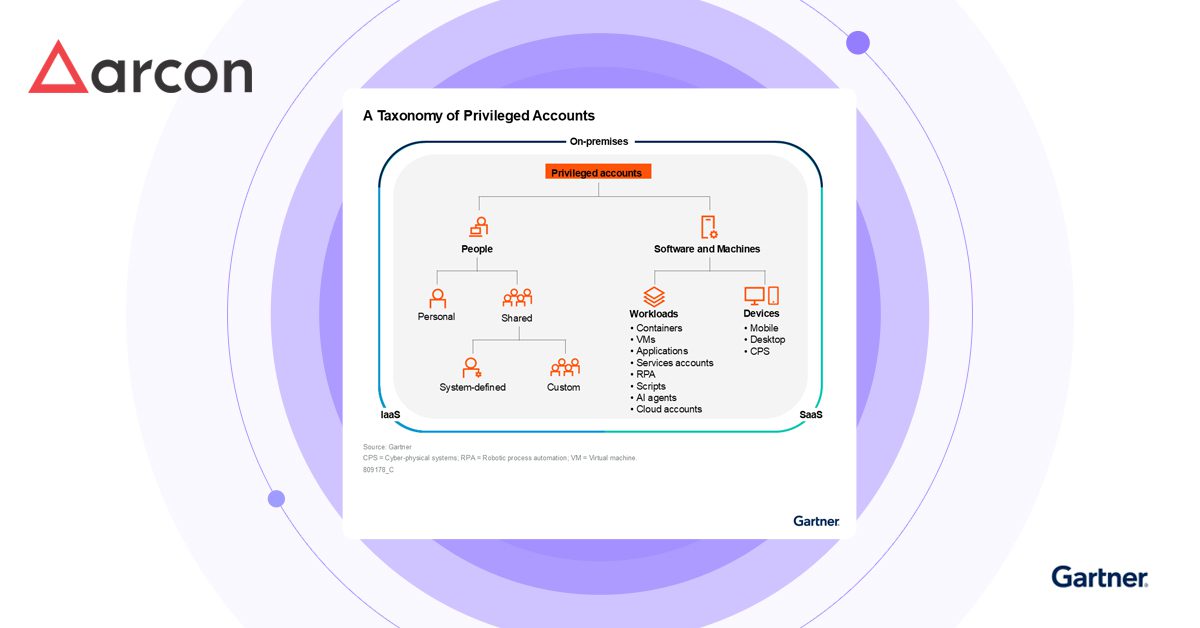
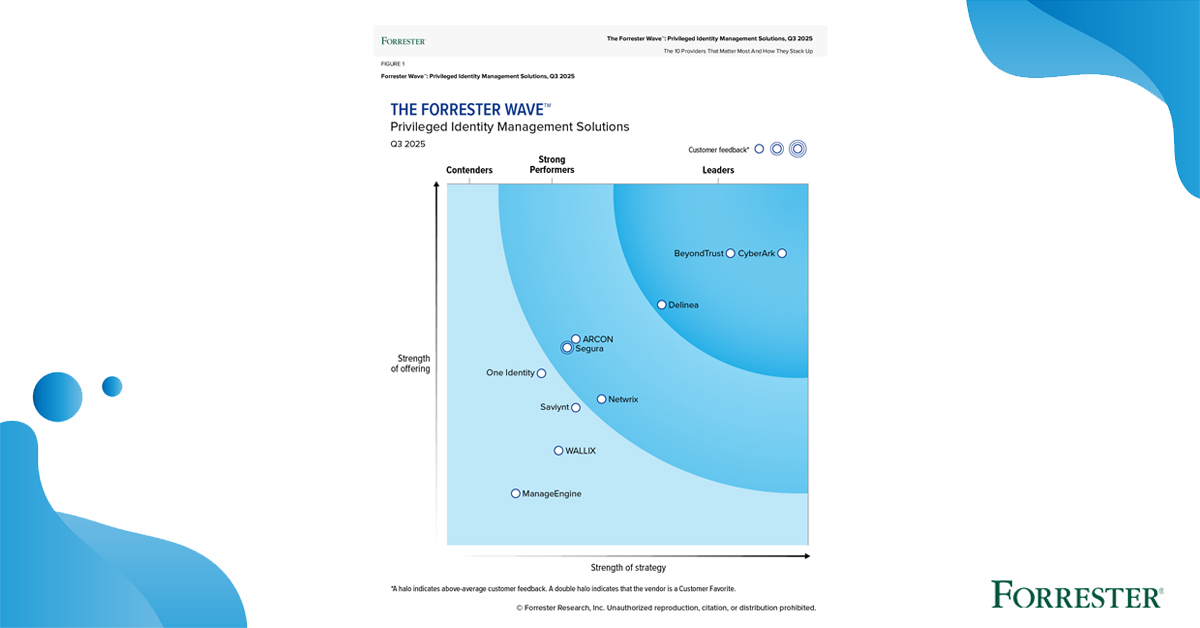
ARCON offers PAM and identity security solutions to reduce IT risks and meet regulatory compliance.
Integrated access management
Cyber Security & Resilience
Secrets Management
Solutions
See how ARCON solutions deliver privileged access security in different industries, meet different compliances and address multiple use cases.
By Industries
By Compliance
Services
Learn about the range of professional training and certifications that ARCON University offers for all IT security aspirants.
SERVICES
Resources
Explore in-depth insights, strategies and trends shaping the future of cybersecurity with ARCON.
Company
Learn about the founding, history, and global reach of ARCON as a company.
Products
Integrated access management
Cyber Security & Resilience
Secrets Management
Solutions
Services
SERVICES